Malicious cyber activities on ICS computers are considered extremely dangerous threats as they could potentially cause material losses and production downtime in the operation of industrial facilities.
In 2018, the share of ICS computers that experienced such activities grew to 47.2% from 44% in 2017, indicating that the threat is rising.
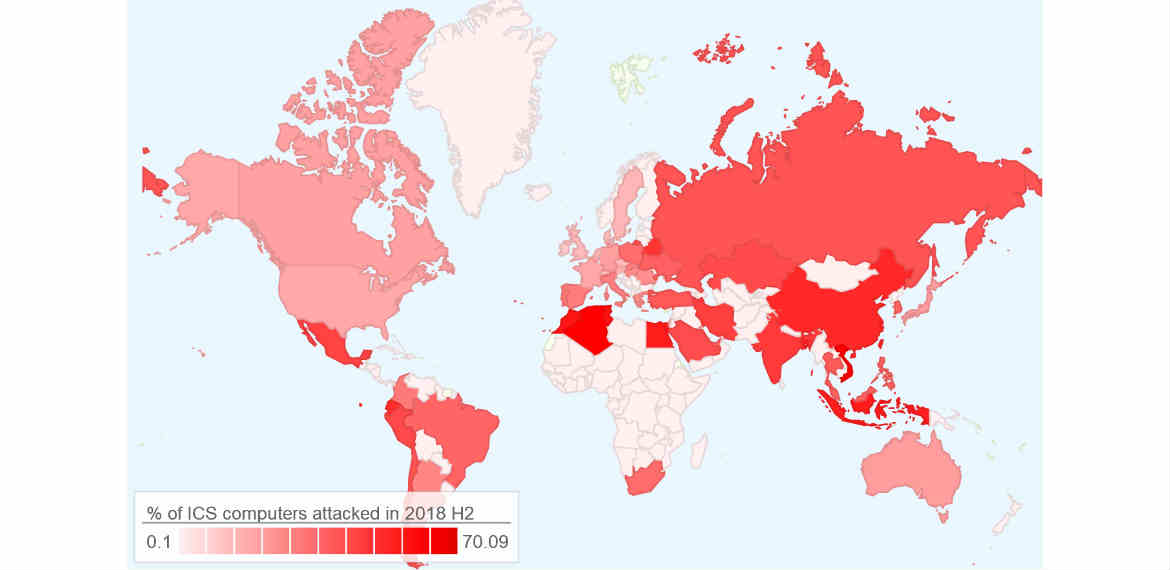
According to the new report, the top three (3) countries worldwide in terms of the percentage of ICS computers on which Kaspersky Lab prevented malicious activity were the following: Vietnam (70.09%), Algeria (69.91%), and Tunisia (64.57%). The least impacted nations were Ireland (11.7%), Switzerland (14.9%), and Denmark (15.2%).
“Despite the common myth, the main source of threat to industrial computers is not a targeted attack, but mass-distributed malware that gets into industrial systems by accident, over the internet, through removable media such as USB-sticks, or e-mails. However, the fact that the attacks are successful because of a casual attitude to cybersecurity hygiene among employees means that they can potentially be prevented by staff training and awareness – this is much easier than trying to stop determined threat actors,” said Kirill Kruglov, security researcher at Kaspersky Lab ICS CERT.
ICS Threats in Southeast Asia and the Philippines
Globally, Southeast Asia is the second top region with the most proportion of ICS computers on which malicious objects were detected and blocked by Kaspersky Lab at 57.8%.
In the region, the Philippines ranked fourth with the most ICS infections that were countered by Kaspersky Lab at 41.6% in the second half of 2018. According to Kaspersky Lab, the top main sources of threats for computers in the industrial infrastructure of organizations in the region are the internet, removable devices and email attachments.
“Regardless of industry, businesses will always have to deal with human error. But it will be more pronounced and threatening for industrial companies responsible for manufacturing and critical operations. From a technology standpoint, it’s worth noting that traditional IT security solutions will no longer be enough to protect industrial networks from these threats. ICS decision makers should now aim for a “True Cybersecurity” which covers four key stages of attacks – predict, prevent, detect, and respond.” said Yeo Siang Tiong, General Manager for Southeast Asia at Kaspersky Lab.
Kaspersky Lab ICS CERT recommends implementing the following technical measures:
• Regularly update operating systems, application software on systems that are part of the enterprise’s industrial network.
• Apply security fixes to PLC, RTU and network equipment used in ICS networks where applicable.
• Restrict network traffic on ports and protocols used on edge routers and inside the organization’s OT networks.
• Audit access control for ICS components in the enterprise’s industrial network and at its boundaries.
• Deploy dedicated endpoint protection solutions on ICS servers, workstations and HMIs, such as Kaspersky Industrial CyberSecurity. This solution includes network traffic monitoring, analysis and detection to secure OT and industrial infrastructure from both random malware infections and dedicated industrial threats.
• Make sure security solutions are up-to-date and all the technologies recommended by the security solution vendor to protect from targeted attacks are enabled.
• Provide dedicated training and support for employees as well as partners and suppliers with access to your network.
• Use ICS network traffic monitoring, analysis and detection solutions for better protection from attacks potentially threatening technological process and main enterprise assets.
Read the full text of the report on Kaspersky Lab ICS CERT website