On the other hand, ransomware Trojans steals users’ files and demands ransom from its victims. The type of malware that targets Android mobile devices are called blockers, which are so named because they block access to the infected device, meaning not only are the files become inaccessible but the entire system is. So an infected Android device will have a screen overlayed with a dodgy banner or demanding a PIN.
Usually a ransomware gets into an Android device when its user opens a malicious attachment, clicks on a suspicious link, installs apps from third-party app stores or clicks on an ad even on a legitimate website.
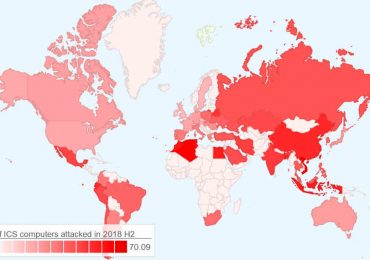
In the Philippines, there have been 30 attempts to install mobile ransomware in Android devices of Kaspersky mobile solution users in nine months this year compared to just 15 last year. Meanwhile, there were already 49 attempts in nine months this year to install mobile banking malware detected in Android devices of Kaspersky customers in the country compared to 46 instances in 2018.
The top five mobile Trojans monitored to have been attempting to infect Android devices of Kaspersky mobile security users in the Philippines for two consecutive years are the following:
| Country | Top 5 type of mobile malware (2018) | Top 5 type of mobile malware (2019) | ||||||||||||||||||||
| PH |
|
|
From Kaspersky data, it shows that Filipino Android mobile users are targets of the Hiddapp mobile malware. This malware family uses advertising as its main monetization method. It secretly downloads ads on to the infected device, displaying as many ads as possible to the Android device user. These Trojans can hide in the system folder which makes them difficult to remove. If the user detects the adware app, the Trojan will prevent the app from being deleted and instead re-install it at the first opportunity.
The Boogr family are Trojans assigned to files recognized as malicious by Kaspersky’s machine-learning tools. The fourth top mobile malware Dvmap is an extremely dangerous Trojan as they use superuser privileges to carry out their malicious activity. They place their components in the device which the Android user only has read access to so these malware cannot be removed using regular system tools. The fifth top mobile malware Agent family covers a wide range of Trojan specimen from various developers.
In 2018, Filipino Android users got a lot of the Dropper mobile malware family, which displays persistent ads and steals money through SMS subscriptions. The Dropper is designed to bypass detection and used by cybercriminals to wrap all sorts of payloads such as banking Trojans, ransomware and adware.
The Triada has similar characteristics as with the menacing Dvmap.
“We can see that attempts to infect Kaspersky mobile users year on year is quite going down in SEA and we attribute that to the growing awareness of the public about protecting their mobile data. The Philippines is hands-down an Android country and combined with the Filipinos’ very strong interest in digital activities, we understand why at number three overall in the region, Filipino Android users remain to be among cybercriminals’ targets,” said Yeo Siang Tiong, general manager for Southeast Asia at Kaspersky.
“We must remember that all users must exert effort in protecting their smartphones especially as they use it increasingly for critical transactions such as online shopping and online banking. With the BYOD being a trend embraced in the country, we also encourage businesses to pay attention on how their employees protect their devices, especially those being used for corporate purpose. For this, we continue working with local partners like Smart and Home Credit in the Philippines to help make mobile security more affordable and accessible to more Filipinos.” he added.
Kaspersky suggests the following ways to spot and avoid Android malware:
● Download apps only from official stores such as Google Play. It won’t provide a full security guarantee, but the risk of encountering a Trojan will be considerably lower. Apps from third party marketplaces are exactly where hackers plant their malware-ridden apps.
● We recommend that you block the installation of software from third-party sources in the device settings. This eliminates randomly downloaded threats that attempt to mimic system updates and the like. Go to Android settings, choose Security and uncheck/disable the “Unknown Sources” box.
● Remember to install system and application updates — they patch vulnerabilities that criminals can exploit.
● Think hard before clicking on dubious links in email or text messages.
● Pay attention to permissions requested by apps during installation. Think about whether they match the purpose of the app. Granting the wrong permissions can send your sensitive data off to third parties.
● Be wary of a free antivirus trial as it could be malware in disguise that can attack your mobile device. Affordable Android security software is available from trusted vendors and effectively does the job of blocking malicious apps.