Each year, the security industry faces new types of threats as cybercriminals evolve their approach toward accessing organizations’ data. As we approach 2017, the security experts at Symantec have taken a close look at the trends we can expect to see this year and in the years ahead. Given the consistently changing security landscape, it’s important to take a moment and determine where the security industry needs to focus their attention as we move into the next year.
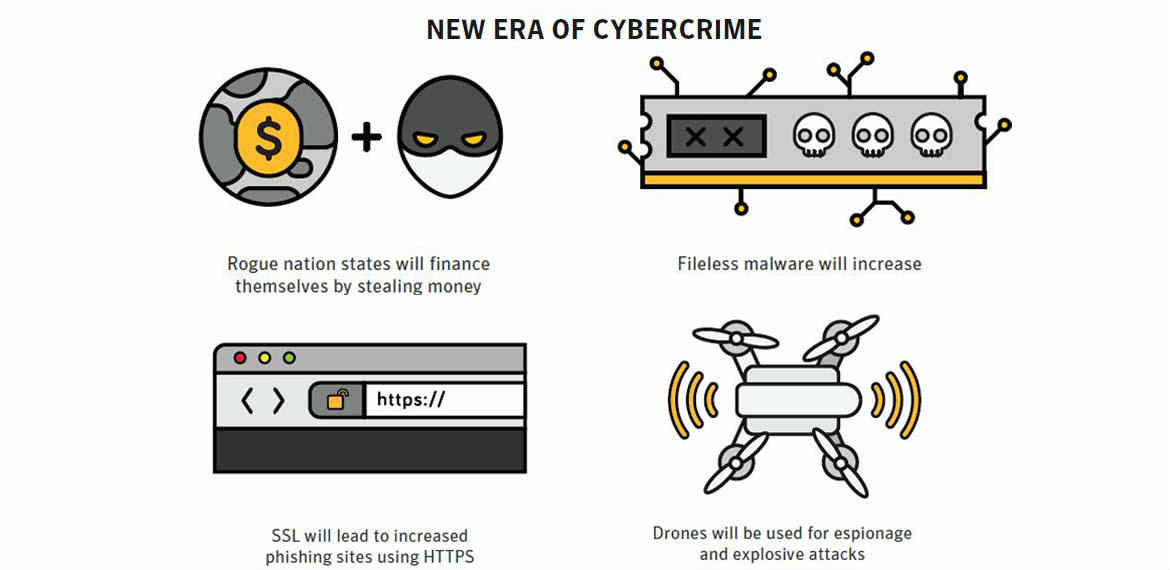
A new era of cybercrime
• Rogue nation states will finance themselves by stealing money online. There is a dangerous possibility that rogue nation states could align with organized crime for their personal gain, such as what we saw in the SWIFT attacks. This could result in down time for countries’ political, military or financial systems.
• Fileless malware will increase. Fileless infections – those written directly onto a computer’s RAM without using files of any kind – are difficult to detect and often elude intrusion prevention and antivirus programs. This type of attack increased throughout 2016 and will continue to gain prominence in 2017, most likely through PowerShell attacks.
• Secure Sockets Layer (SSL) abuse will lead to increased phishing sites using HTTPS. The rise in popularity of free SSL certifications paired with Google’s recent initiative to label HTTP-only sites as unsafe will weaken security standards, driving potential spear-phishing or malware programs due to malicious search engine optimization practices.
• Drones will be used for espionage and explosive attacks. This could be seen in 2017, but is more likely to occur further down the road. By 2025, we can expect to see “dronejacking,” which will intercept drone signals and redirect drones for the attacker’s benefit. Given this possibility, we can also expect to see anti-drone hacking technology being developed to control these devices’ GPS and other important systems.
IoT devices offer new revenue streams for cybercriminals
• Connected cars will be taken for ransom. As cars start to have connected capabilities, it is only a matter of time until we see an automobile hack on a large scale. This could include cars being held for ransom, self-driving cars being hacked to obtain their location for hijacking, unauthorized surveillance and intelligence gathering, or other automobile-focused threats. This will also lead to a question of liability between the software vendor and automobile manufacturer, which will have long-term implications on the future of connected cars.
CONTINUE READING…